3 Lessons From the Facebook and Google Loss of $100M to a Spear Phishing Attack

BBC reported recently that Facebook and Google separately wired over $100 million to a single hacker in Lithuania. While these are global corporate giants, there are lessons for everyone about cybersecurity in 2017.
- A lone hacker can cause a big financial loss
- No matter how sophisticated your cybersecurity defense, you are at risk
- Spear phishing and social engineering bypass network and endpoint security
Cyber Criminals Posing as a Supplier
Facebook and Google really aren’t that special in falling for this type of scam. Not long ago, Ubiquiti networks was swindled out of $47 million based on a similar social engineering attack. The BBC outlined the approach that took down Facebook and Google.
“Fraudulent phishing emails were sent to employees and agents of the victim companies, which regularly conducted multimillion-dollar transactions with [the Asian] company,” the US Department of Justice (DOJ) said in March.
These emails purported to be from employees of the Asia-based firm, the DOJ alleged, and were sent from email accounts designed to look like they had come from the company, but in fact had not.
There you go. Classic spear phishing (definitions of phishing, spear phishing, social engineering and whaling can be found here). Specific employees were targeted with fraudulent emails. The perpetrator doctored documents to look like a legitimate Chinese supplier. Two companies wired $100 million to a lone hacker. The unusual part of the story is that the hacker was caught and some of the funds were recovered. If this were a sophisticated ring like the one that pulled off the Swift wire transfer hacks of the Bangladesh Bank for $81 million, you can bet all of the funds would have been long gone and not available for reclamation.
What’s Wrong Here? Humans are easily fooled.
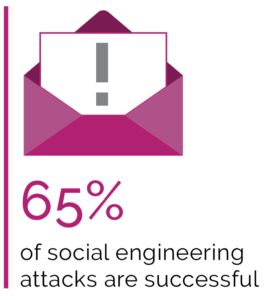
There was a quote from a “security expert” in the article that explains very well why these attacks will continue to occur. He said, “But people are part of the best security you can have – that’s why you have to train them.” Readers of the Graphus blog know that we are supporters of training to help employees identify phishing and spear phishing attacks. However, readers also know that employees trained to spot phishing still open 30% of fraudulent emails. That is likely why 65% of companies reported being victims of successful social engineering attacks last year.
The idea that you can rely on humans to be your firewall against sophisticated cyber scams is outdated wishful thinking. Go ahead and do some training. It may help. But you must recognize that people are easily fooled. Your employees need the help of automation.
Current Cyber Defenses Don’t Stop Spear Phishing Attacks.
Like training, network security and endpoint protection are also necessary defenses. The problem is that social engineering tactics like spear phishing go around those defenses because your employees grant them access. The employee is either duped into doing something on behalf of the hacker posing as a business partner or tricked into revealing credentials that provide direct access to your systems.
A PhishMe study in 2016 found that 91% of cyber attacks started with a phishing attack. The well-referenced Verizon DBIR report of 2015 found that 90% of security incidents were attributable to human failings. Secure your networks and endpoints, but be aware that what the FBI calls Business Email Compromise (BEC) is a widely used cyber attack vector. You just can’t rely on humans to correctly identify all cybersecurity attacks. The cyber attackers do their research and have a high success rate.
What Are You Doing to Protect Your Employees from Spear Phishing?
There are two automated approaches that are being used today to protect employees from spear phishing: DMARC and Trust GraphTM. DMARC helps protect organizations from one type of spear phishing attack. It is better than nothing. However, the Trust Graph pioneered by Graphus protects organizations from all four types of spear phishing attacks. Graphus has a white paper that goes into detail on this (click here).
The Trust Graph uses graph theory and machine learning to rapidly analyze relationships between the external email sender and the receiving employee and also compares other indicators to both externally and internally generated threat intelligence sources. Over a 15-month beta trial with 10 mid-sized businesses, the Graphus Trust Graph successfully identified spear phishing and social engineering attacks. You can activate Graphus in just a minute and trial it for free to see how it works.










