10 Nation-State Cyberattack Facts You Need to Know

Nation-state cybercrime isn’t just a risk for businesses in certain sectors anymore. Advanced Persistent Threat (APT) groups (APTs) have expanded their scope of attack, hitting businesses that weren’t thought to be in danger of that kind of threat in the past. That puts every business at risk as threat actors seek new ways to obtain information, strike targets and make money. These 10 facts nation-state cyberattack facts illustrate today’s climate of risk and offer insights into protecting businesses from nation-state trouble.
Explore today’s biggest threats & what’s next in The State of Email Security 2022 GET IT>>
What is a Nation-State Cyberattack?
Microsoft defines nation-state cybercrime as malicious cyberattacks that originate from a particular country to further that country’s interests. It’s a complex subject that is full of twists and turns, and just like any other field, it also has some very specific terminology.
Nation-State Threat Actor —- Nation-state threat actors are people or groups who use their technology skills to facilitate hacking, sabotage, theft, misinformation and other operations on behalf of a country. They may be part of an official state apparatus, members of a cybercrime outfit that are aligned with or contracted by a government or freelancers hired for a specific nationalist operation.
Advanced Persistent Threat (APT) —- These are nationalist cybercrime outfits with sophisticated levels of expertise and significant resources that work to achieve the goals of the government that supports them, undertaking defined operations with specific goals that forward the objectives of their country.
Infrastructure Attack —– When nation-state actors conduct an infrastructure attack, they’re attempting to damage one of their country’s adversaries by disrupting critical services like power, water, transportation, internet access, medical care and other essential requirements for daily life. Infrastructure attacks are a major component of modern spycraft and warfare.
Learn how incident response planning boosts cyber resilience & security. GET THE EBOOK>>
10 Nation-State Cyberattack Facts You Must See
- An estimated 90% of Advanced Persistent Threat Groups (APTs) Groups regularly attack organizations outside of the government or critical infrastructure sectors.
- There was a 100% rise in significant nation-state incidents between 2017 and -2021.
- Russian nation-state actors are increasingly effective, jumping from a 21% successful compromise rate in 2020 to a 32% rate in 2021.
- 21% of nation-state attacks in 2021 targeted consumers.
- 79% of nation- state attacks in 2021 targeted enterprises.
- 58% of all nation-state attacks in the last year were launched by Russian nation-state actors.
- Ransomware is the preferred weapon of nation-state threat actors.
- The “big 4” sponsors of APTs are Russia, China, North Korea and Iran.
- Nine in 10 (86%) organizations believe they have been targeted by a nation-state threat actor.
- The average nation-state-backed cyberattack costs an estimated $1.6 million per incident.

See 10 reasons why Graphus is just better than other email security solutions. SEE THE LIST>>
Common Targets of Nation-State Attacks
Researchers took a look at nation-state attacks and determined who APTs were going after the most.
| Targets of Nation-State Cyberattacks | % of Total |
| Enterprises | 35% |
| Cyber Defense Assets | 25% |
| Media & Communications | 14% |
| Government Bodies | 12% |
| Critical Infrastructure | 10% |
Source: Dr. Mike McGuire and HP, Nation States, Cyberconflict and the Web of Profit
Are you ready to stop ransomware? Find out with our 5 Steps to Ransomware Readiness infographic! GET IT>>
Nation-State Cyberattack Facts About Attack Vectors
Nation-state threat actors will use a wide variety of means to accomplish their goals, but nation-state cyberattack facts offer insights into their go-to attacks employed against both public and private sector targets.
Phishing Attack —- A technique for attempting to persuade the victim to take an action that gives the cybercriminal something that they want, — like a password — or accomplishes the cybercriminal’s objective, — like infesting a system with ransomware through a fraudulent solicitation in email or on a web site.
Distributed Denial of Service (DDoS) Attack -— Distributed Denial of Service attacks are used to render technology-dependent resources unavailable by flooding their servers or systems with an unmanageable amount of web traffic. This type of attack may be used against a wide variety of targets like banks, communications networks, media outlets or any other organizations that rely on network resources.
Malware Attack —- Malware is a portmanteau of “malicious software.” It is commonly used as a catch-all term for any type of malicious software designed to harm or exploit any programmable device, service or network. Malware includes trojans, payment skimmers, viruses and worms.
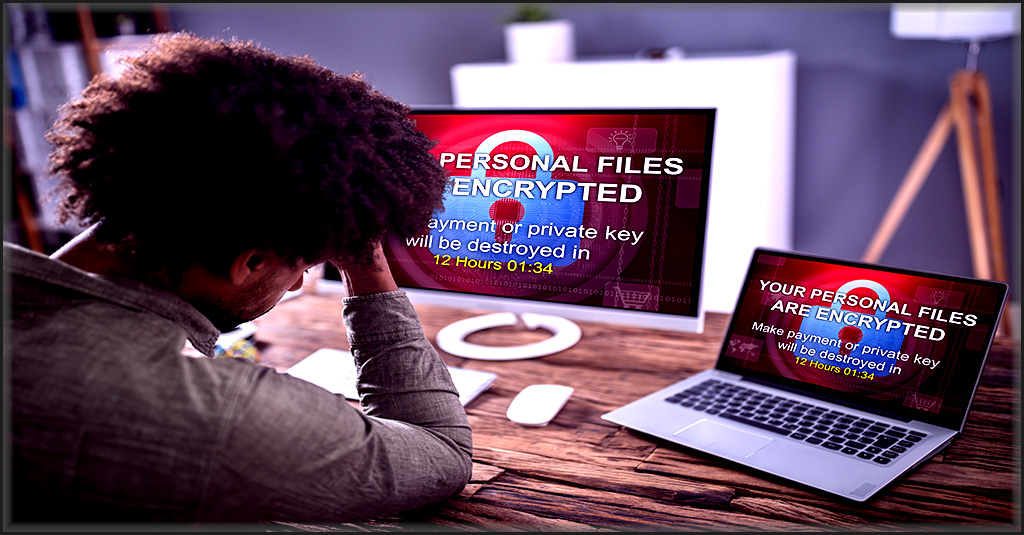
Ransomware Attack -— Ransomware is the favored tool of nation-state cybercriminals. This flexible form of malware is designed to encrypt files, lock up devices and steal data. Ransomware can be used to disrupt production lines, steal data, facilitate extortion, commit sabotage and a variety of other nefarious purposes. Ransomware attacks are highly effective and can be used against any organization.
Backdoor Attack —– Nation-state threat actors will often intrude into an organization’s systems and establish a foothold called a back door that allows them to return easily in the future. It could be months or years before they use it. This also affords them the opportunity to unobtrusively monitor communications, copy data and find vulnerabilities that enable further attacks.

Follow the path business takes to a ransomware disaster in The Ransomware Road to Ruin. DOWNLOAD IT NOW>>
These Nation-State Cyberattack Facts Make it Clear That Strong Email Security Iis the Cornerstone of a Powerful Defense
Protecting your company from phishing is essential to reduce the chance of falling victim to a nation-state cyberattack. You need strong email security to get the job done —– and you can get it at a great price.
Enter Graphus. This email security powerhouse uses AI to keep phishing emails away from user inboxes automatically. Automated email security is 40% more effective at spotting and stopping dangerous phishing messages than traditional email security or a SEG. Graphus is also budget-friendly at half the price of its competitors.
You’ll benefit from:
- A powerful guardian that protects your business from some of today’s nastiest email-related threats like cryptomining, spear-phishing, business email compromise, ransomware and other horrors.
- The power of TrustGraph, our patented technology that uses AI to compare more than 50 separate data points to analyze incoming messages and spot illegitimate messages quickly and efficiently before they land in anyone’s inbox.
- A solution that uses machine learning to add information to its knowledge base with every analysis it completes to continually refine your protection and keep learning without human intervention.
See how to avoid cybercriminal sharks in Phishing 101. DOWNLOAD IT>>










