Successful White House Spear Phishing Attacks Show No One is Safe
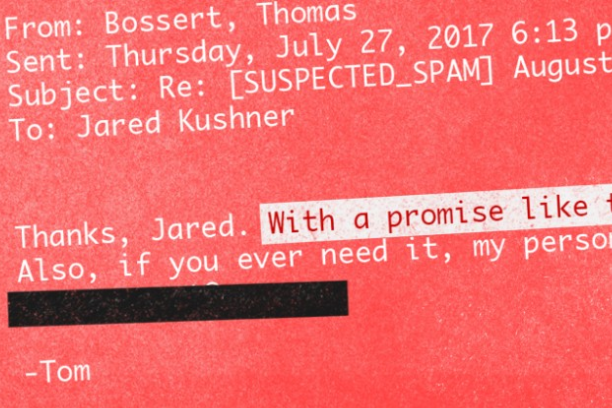
No one is safe from spear phishing attacks. Not even the highest-ranking government officials. CNN reported recently that a self-described email prankster successfully spear phished several members of the White House staff and First Family posing as the President’s son-in-law and advisor, Jared Kushner. One victim was Homeland Security Adviser Tom Bossert:
“Tom, we are arranging a bit of a soirée towards the end of August,” the fake Jared Kushner on an Outlook account wrote to the official White House email account of Homeland Security Adviser Tom Bossert. “It would be great if you could make it, I promise food of at least comparible (sic) quality to that which we ate in Iraq. Should be a great evening.”
Bossert wrote back: “Thanks, Jared. With a promise like that, I can’t refuse. Also, if you ever need it, my personal email is” (redacted).
Yes, not only did Bossert, who holds one of the highest security positions in the country, fall victim to a spear phishing scheme, he also provided his personal email address unsolicited. Even the email prankster was “surprised Bossert responded given his expertise” according to CNN.
Everyone is Vulnerable
But, he’s not alone. The same email prankster also targeted another White House Official, former Communications Director Anthony Scaramucci posing as former White House Chief of Staff Reince Priebus writing:
“I had promised myself I would leave my hands mud free,” wrote the fake Priebus, “but after reading your tweet today which stated how; ‘soon we will learn who in the media who has class, and who hasn’t’, has pushed me to this. That tweet was breathtakingly hypocritical, even for you.”
Even though the email was from an unauthorized mail.com account, Scaramucci still fell for the spear phishing scheme because of its content. The cyber criminal used information from the media and the victim’s own Twitter account to fool him into responding. Unlike phishing, spear phishing is a targeted attack. Cyber criminals use information made readily available on the internet and through social media to gain a victim’s trust and fool them into doing their bidding.
It Could Have Been Worse
These White House officials were very lucky that this spear phishing attack was for the criminal’s own amusement and not for nefarious motives. Other spear phishing victims have not been quite as lucky. The consequences of a successful spear phishing attacks can cost a company millions. One such victim was Ubiquiti Networks, as the Infosec Institute reports:
“The potential destructiveness of a spear phishing attack for a business is shown clearly in the case of Ubiquiti Networks Inc., an American network technology company for service providers and enterprises. In June of 2015, the company lost $46.7 Million because of a spear phishing e-mail. A report by the U.S. Securities and Exchange Commission shows that the attack was carried through ‘employee impersonation and fraudulent requests from an outside entity targeting the Company’s finance department.’”
Even tech titans are at risk. Facebook and Google wired over $100 million to a single hacker in Lithuania according to BBC.
“Fraudulent phishing emails were sent to employees and agents of the victim companies, which regularly conducted multimillion-dollar transactions with [the Asian] company,” the US Department of Justice (DOJ) said in March. These emails purported to be from employees of the Asia-based firm, the DOJ alleged, and were sent from email accounts designed to look like they had come from the company, but in fact had not.”
How to Stop Spear Phishing

Most cyber attacks begin with a successful spear phishing email because as demonstrated, they work. Humans are vulnerable and attackers know it. If a highly trained individual like White House Homeland Security Adviser Tom Bossert is susceptible to these types of attacks, how can organizations expect their employees not to fall for the same tactics? Employee training can help reduce the risk of a successful spear phishing attack but it cannot completely prevent it. Companies cannot rely on a human firewall. It is not fool proof. Graphus has stepped in to directly address the problem of spear phishing.
Graphus automatically detects suspicious emails by creating a Trust Graph™ between people, devices and networks that is unique to each organization. It’s like a Touch ID for a company’s inbox. With Graphus, you don’t have to hope your employees can detect a spear phishing email because it can flag them before reaching users see them.
The White House spear phishing incidents demonstrate that humans really are the weakest link when it comes to cyber crime. Graphus eliminates this risk and it only takes about a minute to get started. Click the button below to start your free trial today.










