What Is the Goal Behind Phishing Emails?

The advent of the internet has given bad actors a new avenue for fraud. Knowing cybercriminals’ motives and methods for launching phishing attacks is essential to avoid their traps.
Get the guide that helps you detect & defeat dangerous BEC attacks to keep your company out of trouble! DOWNLOAD IT>>
What is the goal behind phishing emails?
The goal behind phishing attacks is for cybercriminals to persuade their victims to act in some way that benefits the bad actors, like sending money, handing over a password, downloading malware or giving the bad guys sensitive data. Perpetrators often use social engineering techniques to conceal their identities and motives, presenting themselves as trusted individuals or information sources to fool the victim into believing their lies. Many of these social engineering exploits create a sense of urgency and rely on people’s willingness to be helpful or fear of punishment as a manipulation tactic. While every phishing attack is different, there are some common themes to watch out for to avoid becoming a victim.
Financial theft
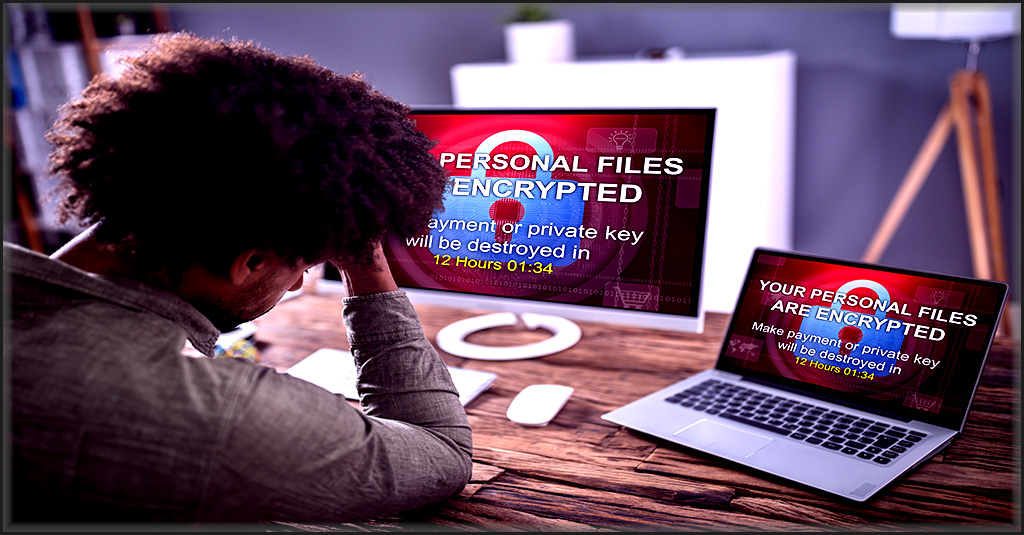
The most prominent consequence of phishing is financial loss. Scammers commit financial theft through ransomware attacks, extortion and fraudulent funds transfer. This is usually the motive of a phishing attack that results in a business email compromise (BEC) or ransomware attack.
Data theft
Data is the new oil for organizations. Every business has valuable data at its disposal that helps it conduct business. Cybercriminals go after an organization’s data to sell it for profit or ransom it back to the organization. Sometimes, the data cybercriminals obtain in one cyberattack is used to fuel another, a circumstance often seen in supply chain attacks. Bad actors typically obtain data through unauthorized access, dark web forums and unintentional information sharing.
Identity theft
In many successful cyberattacks, hackers gain access to peoples’ sensitive personally identifiable information (PII), or protected health information (PHI). PII helps bad actors commit identity theft. Identities can be used to facilitate further cybercrime or sold on the dark web.
Now that we know the consequences of a cyberattack, it is essential to understand how cybercriminals lure their targets.
Learn how incident response planning boosts cyber resilience & security. GET THE EBOOK>>
What do phishing emails try to get you to do?
A typical phishing email uses one of two methods to do its dirty work. Sometimes, an email carries a malicious attachment that, when downloaded, installs malware like ransomware. In other cases, a phishing email contains a link to a website that cybercriminals can use to steal information like passwords or trick users into downloading malware.
There are a variety of methods through which scammers execute their devious plans. Here are some common ways phishing emails go from being an attempt to a successful attack.
Click a link
Cybercriminals send convincing emails that compel the victims to click a link in the emails triggering a malicious download, and giving cybercriminals access to the victims’ data and systems. Brand impersonation and spoofing are common techniques used in this type of attack.
Visit a website
If the phishing email asks the victim to visit a website, the goal is often to steal information like passwords to give cybercriminals a gateway to enter their business or personal system to steal information or deploy malware.
Open an attachment
Some messages deliver a malicious payload through an attachment that comes with a phishing email. As these emails seemingly come from a trusted source, victims open the attachment and fall into the cybercriminal’s carefully laid trap. This is a technique often used in BEC and malware attacks.
Enter information
Another devious method through which cybercriminals can access information is through an embedded form within a malicious website that asks users to enter their credentials. Once users enter the desired information, hackers can steal their credentials and launch an account takeover attack (ATO).
Reply directly
Bad actors sometimes disguise themselves as trusted colleagues, business executives or someone’s regular correspondent in order to trick a victim into providing sensitive information. Conversation hijacking, in which cybercriminals interject themselves in an already extant conversation thread, is an example of this type of attack.
Take action
Sometimes, phishing perpetrators pose as an authority figure, like an executive at the victim’s company or a government official, and ask the victims to provide access to a system or send money to them directly. Hackers create a sense of urgency, which does not give victims ample time to check the sender’s authenticity.
Are you ready to stop ransomware? Find out with our 5 Steps to Ransomware Readiness infographic! GET IT>>
What type of information do phishing emails seek to obtain?
Phishing attacks are launched to obtain money, data and credentials. Phishing attacks on individuals may be highly targeted, a technique called spear phishing. In more general phishing attempts, cybercriminals cast a wide net, creating and using a lure that appeals to a wide variety of people to see what they can get.
Cybercriminals are interested in obtaining various types of information, such as:
Personal information
If a phishing email focuses on a specific individual, the attackers often tailor an email to speak directly to the victim and include information only an acquaintance would know. The following information is most sought-after in a phishing attack on an individual:
- Social Security Number: This information may be used for identity theft, fraudulent loan or credit card applications.
- Bank accounts: Once cybercriminals have access to someone’s bank accounts, they use them for money transfers and financial manipulation.
- Credit card numbers: Stealing someone’s credit card information is an ideal way for bad actors to purchase products and services online.
- Tax information: Hackers use your tax information to steal tax refunds. In one year, hackers successfully stole sensitive information from over 100,000 taxpayers using the U.S. Internal Revenue Service’s Get Transcript service. They used this data to file fraudulent tax returns, stealing an estimated $50 million in tax refunds.
- Personal files or photos: We all have private images, files or videos on our devices. If hackers get their hands on these personal files, they use them for blackmail or sell them illegally.
- Login credentials: Every individual has a significant online presence today, and we use the same passwords for many online accounts. Cybercriminals gain access to various accounts if they steal one of your login credentials. This information is used to facilitate further cyberattacks or sold on dark web forums. More than 60% of employees use the same password across multiple work and home applications.
While a leak of personal information has dire consequences for an individual, compromising business information has catastrophic consequences. According to the United States Securities and Exchange Commission (SEC), about 60% of SMBs go out of business within six months of a data breach or cyberattack. Here is the business information that cybercriminals seek from their phishing attacks.
Business information
Cybercriminals will steal any information that they can, but these types are some of their favorites.
- Login credentials: If cybercriminals have access to an employee’s login credentials, they can easily access business accounts and commit data theft. The average organization is likely to have about 17 sets of login details available on the dark web for malicious actors to use.
- Corporate bank accounts: Gaining access to corporate banking information allows scammers to use them for money transfers and financial manipulation.
- Business files: Every business has some highly confidential business files, which could be damaging for the business and its clients if they fall into the wrong hands. After accessing those files, cybercriminals could hold them for ransom, use the information within other cyberattacks or sell them illegally.
- Internal communications: An organization’s internal communications can contain a lot of sensitive information. Perpetrators can use it to carry out several criminal activities, including extortion.
- Proprietary information: Similar to business files, cybercriminals can hold proprietary information for ransom, sell it to competitors or use it to steal intellectual property.
- Customer and employee data: Customer and employee data are in high demand on many dark web forums. Attackers steal this data to sell it on the dark web and may also use it to tarnish a company’s reputation.

Follow the path business takes to a ransomware disaster in The Ransomware Road to Ruin. DOWNLOAD IT NOW>>
Protect your organization from phishing with Graphus
As the world’s first AI-driven email security solution, Graphus automatically protects organizations from email-based ransomware attacks. Graphus creates a wall between organizations and cyberattacks by automatically monitoring communication patterns between people, devices and networks to reveal untrustworthy emails.
- Graphus blocks sophisticated phishing messages before users see them.
- Puts three layers of protection between employees and dangerous email messages.
- Seamlessly deploys to Microsoft 365 and Google Workspace via API without big downloads or lengthy installs.
- No MX record changes, email traffic rerouting or threat intelligence uploads needed.
- Intuitive reporting helps companies gain insight into the effectiveness of their security, level of risk, most common attack types and more.
- Get powerful email security and serious protection from phishing at half the cost of the competition.
If you wish to know more about Graphus, book a demo here.










