Who Falls for Phishing?
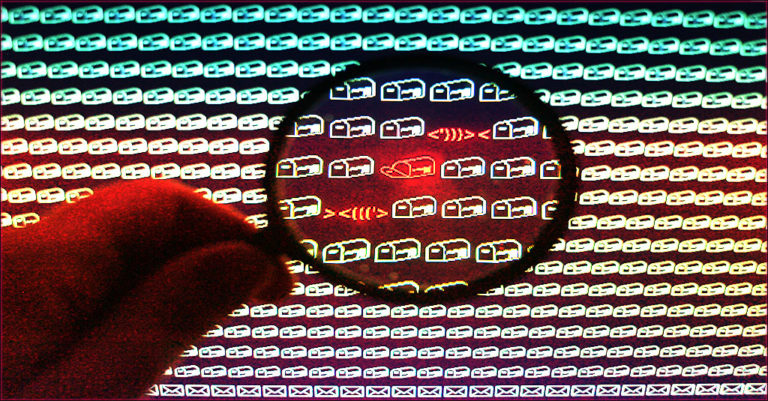
Phishing is the biggest risk that every business faces today. The precursor to disasters like business email compromise, a data breach or a ransomware attack, phishing packs a punch that can send any business reeling. In order to accomplish their goals, cybercriminals rely on social engineering to trick employees into taking actions that could unleash a cyberattack, and 85% of social engineering actions take place over email. Paying attention to who is likely to fall for cybercriminal tricks can help businesses keep phishing from catching any of their employees.
Learn the secret to ransomware defense in Cracking the RANSOMWARE Code. GET BOOK>>
Learn from These Cybersecurity Disasters
When you look at the most damaging cyberattacks in history, you’ll see that the majority of them have one thing in common: their point of origin was a phishing email. Like these massive cybersecurity disasters in 2020 that were launched with just one fatal click.
An epic Twitter breach resulted in the temporary takeover of more than 130 carefully chosen accounts, including celebrity accounts with massive amounts of followers like Barack Obama, Bill Gates and Elon Musk. The attackers were then able to swindle $121,000 in Bitcoin through nearly 300 transactions by tweeting about a phony investment scheme – and it all started with a 16-year-old cybercriminal posing as a contractor phishing a privileged password from an administrator.
Cybersecurity giant SolarWinds experienced an intrusion by Russian nation-state cybercriminals who were then able to attach a few snippets of code on a routine patch. The patch was then distributed to and downloaded by major US government agencies and national security assets open backdoors that gave the threat actors access to their systems and data for more than 6 months undetected. The breach was initially discovered by cybersecurity experts at FireEye and was determined to have started with a spear-phishing email.
A monster ransomware attack hit Blackbaud, the leading developer of software used by nonprofits for fundraising and administration, is still reverberating over a year later. The attack rocked more than 120 non-profits including Britain’s National Trust, Human Rights Watch and National Public Radio. Adding to the complexity, Blackbaud’s platform was used by many hospitals for fundraising, making this the biggest healthcare cyberattack in history. The point of entry for the ransomware was a phishing email.
See how to avoid cybercriminal sharks in Phishing 101. DOWNLOAD IT>>
Phishing Volume and Cost is Higher Than Ever
More email coming into businesses means more phishing messages that could land in an employee’s inbox, and any phishing message that an employee receives has the chance of spawning a data breach. An estimated 306.4 billion emails were sent and received each day in 2020, triple the average increase of past years. That figure is expected to continue to grow steadily as companies continue to grapple with the implications of the ongoing pandemic and virus variants that could lead to long-term remote work becoming the norm. If email volume continues to trend the way that experts expect, it is estimated to reach over 376.4 billion daily messages by 2025.
The 2021 Ponemon Cost of Phishing Study shed light on the massive revenue hits that companies can suffer in the wake of a successful phishing attack. The biggest takeaway from this report is the colossal increase in the cost of a phishing attack for businesses. Researchers say that the cost of phishing attacks has almost quadrupled over the past six years, with large US companies losing an average of $14.8 million annually (or $1,500 per employee) to phishing. That’s without adding the expense of dealing with an incident investigation or paying a ransom if that email contains ransomware (which is not always legal).
See how ransomware rocks businesses in The Ransomware Road to Ruin. DOWNLOAD IT NOW>>
Phishing Risk Factors Add Complexity
While every business is at risk of a phishing attack every day, some industries are a little more vulnerable than others. A 2020 user behavior study shows that employees in these sectors are the most likely to interact with a phishing email.
The Top 5 Sectors in Which Employees Interact with Phishing Messages
- Consulting
- Apparel and accessories
- Education
- Technology
- Conglomerates/Multi-Nationals
In which industries will cybercriminals find the people who are most likely to submit credentials or share information? These are the top 5 most vulnerable industries:
The Top 5 Sectors in Which Phishing Leads to Credential Compromise
- Apparel and accessories
- Consulting
- Securities and commodity exchanges
- Education
- Conglomerates/Multi-Nationals
A recent experiment by Canadian security researchers exposed the sad truth: an estimated 25% of North American workers tested were fooled by phishing emails, leading to some dangerous consequences.
- 67% of clickers (13.4% of overall users) submitted their login credentials, up substantially from 2019 when just 2% submitted their credentials
- The Public Sector and Transportation workers struggled the most, posting a click rate of 28.4%
- The Education, Finance and Insurance sectors performed considerably better than others, with click rates of 11.3% and 14.2% (tied)
- Users in North America struggled the most with the phishing simulation, posting a 25.5% click rate and an 18% overall credential submission rate
- About 7 out of every 10 clickers willingly compromised their login data
- Users in Europe exhibited lower click and submission rates of 17% and 11%, respectively
An estimated 97% of employees in a wide array of industries are unable to recognize a sophisticated phishing email. So what are they most likely to do when they receive a phishing message?
- 1 in 3 employees are likely to click the links in phishing emails
- 1 in 8 employees are likely to share information requested in a phishing email
- 60% of employees opened emails they weren’t fully confident were safe
- 45% click emails they consider to be suspicious “just in case it’s important.”
- 45% of employees never report suspicious messages to IT for review
- 41% of employees failed to notice a phishing message because they were tired
- 47% of workers cited distraction as the main factor in their failure to spot phishing attempts
See the tide of phishing rise & fall to spot future trends in the eBook Fresh Phish. GET IT>>
AI Doesn’t Get Fooled by Phishing or Social Engineering
Stop phishing with Graphus – the most simple, automated & affordable phishing defense available.
TrustGraph is the star of the show when it comes to keeping potentially dangerous email away from staffers.
- Your first layer of defense against phishing, TrustGraph uses more than 50 separate data points to analyze incoming messages completely before allowing them to pass into employee inboxes.
- TrustGraph also learns from each analysis it completes, adding that information to its knowledge base to continually refine your protection and keep learning without human intervention.
Graphus makes it easy for your employees to report suspicious messages and get help in case of trouble.
- EmployeeShield adds a bright, noticeable box to messages that could be dangerous, empowering staffers to report that message with one click for administrator inspection.
- Phish911 makes it a snap for employees to report any suspicious message that they receive. When an employee reports a problem, the email in question isn’t just removed from that employee’s inbox — it is removed from everyone’s inbox and automatically quarantined for administrator review.
SEE OUR 3 SHIELDS EXPLAINED IN AN INFOGRAPHIC=>
What’s next in phishing? Find out in the 2021 State of Email Security Report! GET IT NOW>>










