These Email Security Trends Offer a Glimpse into the Next Generation of Threats

The state of email security is constantly in flux. However, the evidence is clear that companies are facing an unprecedented flood of phishing attacks that can make an organization’s state of email security perilous. Cybercrime trends, especially around email-based cyberattacks, are major risk drivers. We’ve seen the proof in the recent trend toward more business email compromise attacks as law enforcement activity puts the squeeze on ransomware gangs. While it can be tricky to determine what’s next in cybercrime, today’s cybercrime trends didn’t just pop up out of the blue. These major phishing-related email security trends have been instrumental in shaping the current state of email security and exploring them can offer a glimpse into tomorrow’s email security risks.
Excerpted in part from the cybercrime report The Global Year in Breach 2022. READ THE REPORT>>
Ransomware Gangs are Choosing More Strategic Targets
Cybercriminals evolved their ransomware tactics, targets and technology to make 2021 a good year for them but a bad year for industrial organizations like manufacturers and oil companies. These targets are especially juicy for the bad guys because industrial and utility companies cannot typically afford any delays in their operations. Organizations that fall victim to a ransomware attack lose an estimated average of six working days, and 37% of them experience downtime of one week or more, making heavy industry and infrastructure companies likely to pay up. When looking at the picture of industrial targets most commonly attacked by ransomware gangs in 2021, the evidence shows that manufacturing is at the top of the cybercriminal hit list, followed by energy and transportation are firmly in cybercriminal sights.
Which Industries Experienced the Most Ransomware Attacks in 2021?
| Industry | % of Total |
| Manufacturing | 61% |
| Oil & Gas | 11% |
| Transportation | 10% |
| Utilities | 10% |
| Mining | 7% |
| Heavy & Civil Engineering | 1% |
Source: IBM X-Force Threat Intelligence Index 2021
See 10 reasons why Graphus is better than other email security solutions. SEE THE LIST>>
Ransomware Risk Waxes and Wanes by Sector
In the 2021 FBI Internet Crime Complaint Center (IC3) report, FBI analysts disclosed that IC3 received more than 2,000 ransomware complaints, with more than $16 million in losses — a 20% increase in reported losses compared to the same period in 2020. Some industries had it a little bit harder than others. Banking and Finance got absolutely hammered in Q1 and Q2 2021, with a 1,318% increase in the number of ransomware attacks waged against that sector. That pressure leveled off in the second half of the year. Ultimately, almost one-quarter of attacks in 2021 were aimed at banking and finance targets.
The Top 10 Sectors for Ransomware Attacks
| Industry | % of total recorded attacks in 2021 |
| Banking and Finance | 22% |
| Utilities | 20% |
| Retail | 16% |
| Education | 9% |
| Government | 8% |
| Industrial | 4.8% |
| Outsourcing and Hosting | 4% |
| Construction | 3.6% |
| Insurance | 3% |
| Wholesale | 1% |
| Other | 8.6% |
Source: Trellix
See how ransomware rocks businesses in The Ransomware Road to Ruin. DOWNLOAD IT NOW>>
Nation-State Cybercrime is Everyone’s Problem
Nation-state cyberattacks are no longer a problem for just the public sector. Microsoft says that an estimated 90% of nation-state cybercrime groups regularly attack organizations outside of the government or critical infrastructure framework. In fact, private enterprises are the targets of 35% of nation-state cyberattacks. Russia, North Korea, Iran and China are the four major players in the nation-state cybercrime space, with Russia responsible for 58% of all nation-state attacks in the past year. In fact a recent study by the Center for Strategic and International Studies (CSIS) revealed that nearly nine in 10 (86%) organizations believe they have been targeted by a nation-state threat actor.
Nation-state cyber threats are something that organizations in every sector will have to be prepared to deal with long term. As the world becomes increasingly interconnected and cloud-driven, threat actors will have more reason and more opportunity to strike targets that fall well outside their prior theaters of operation. The bad guys are getting better at pulling off successful operations as well. Russian nation-state actors are increasingly effective, jumping from a 21% successful compromise rate in 2020 to a 32% rate in 2021 – and every increase in that percentage is a loss for public and private sector organizations around the world.
Top 5 Sectors Targeted in Nation-State Attacks
| Targets of nation-state cyberattacks | % of total attacks recorded |
| Enterprises | 35% |
| Cyber Defense Assets | 25% |
| Media & Communications | 14% |
| Government Bodies | 12% |
| Critical Infrastructure | 10% |
| Other | 4% |
Source: Dr. Mike McGuire and HP, Nation States, Cyberconflict and the Web of Profit
Explore today’s biggest threats & what’s next in The State of Email Security 2022 GET IT>>
High Email & Phishing Volume Brings More Security Stress & Bigger Bills
In today’s digital working world, employees rely on email to get the job done, especially when working remotely. That’s a big reason why overall email volume is on the upswing, following a consistent pattern of rapid and significant growth every year.
Email Volume (Estimated in billions)
| 2020 | 306.4 |
| 2021 | 319.6 |
| 2022 | 376.4 (projected) |
Source: Statista
An increase in email volume brings an increase in email phishing volume in its wake, adding stress for the already overtaxed IT staff at most companies from a sea of improperly quarantined emails to adjudicate and false positive email security alerts.
- In January 2021, The U.K. Information Commissioner’s Office (ICO).recorded 150,317 total phishing attacks.
- That number spiked by 2,650% in December 2021, when researchers recorded 4,135,075 total attacks in December 2021.
- In Q1 2022, researchers announced that they’d recorded one million unique phishing attacks in a single quarter for the first time.
Businesses are paying more for security these days because of phishing even if they don’t fall victim to an attack, and that uptick in expense shows no sign of stopping. The 2021 Ponemon Cost of Phishing Study shed light on the colossal increase in the cost of a phishing attack for businesses.
- The cost of phishing attacks has almost quadrupled over the past six years.
- Large U.S. companies lose an average of $14.8 million annually (or $1,500 per employee) to phishing-related expenses.
- On average, companies lose seven hours of productivity per employee to phishing every year.
- Phishing costs businesses more than 10,000 hours of tech time yearly.
AI is the secret weapon you’re looking for to boost business email security. SEE WHY>>
Phishing Attacks Aren’t One-Size-Fits-All
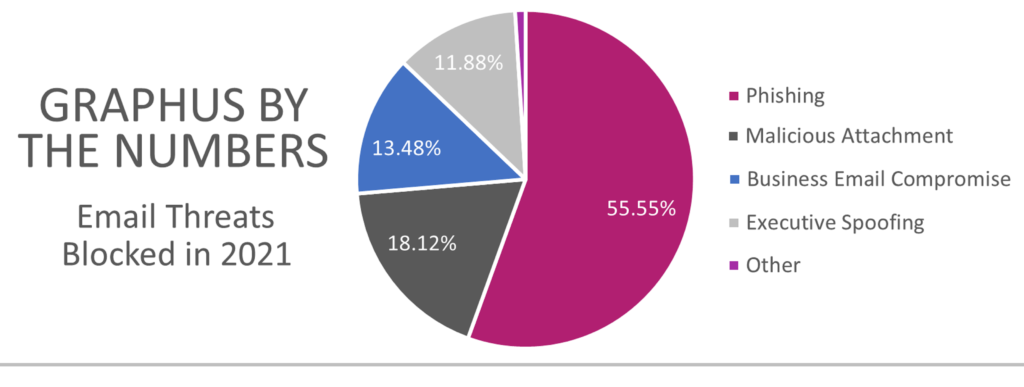
Cybercriminals perpetrate a wide variety of types of phishing attacks. That can make it very challenging for a SEG or conventional security to keep up with changing threat types. But AI-powered solutions don’t have that problem. Graphus uses machine learning to power AI that detects and quarantines most suspicious messages automatically. Graphus’ proprietary technology, TrustGraph, thoroughly analyzes the content of every incoming email an organization protected with the solution receives. Phishing messages are detected and subsequently quarantined. By taking a look at the types of phishing attacks that Graphus spotted and stopped in 2021, it’s easy to see the dangers that companies face from phishing this year and moving forward.
Learn the secret to ransomware defense in Cracking the RANSOMWARE Code. GET BOOK>>
Graphus Stops Email-Based Cyberattacks Cold
Graphus improves any organization’s data security immediately. Choose AI-powered, automated email security to quickly and efficiently protect your company from some of today’s nastiest phishing-related cyberattacks and you’ll enjoy the peace of mind that comes from knowing that you’re blocking 99.9% of sophisticated phishing messages before they ever reach an employee inbox.
- Forget old-fashioned safe sender lists. Graphus analyzes the content of messages using more than 50 points of comparison to suss out fakes fast.
- Cloud-native security harnesses machine learning to inform AI using a patented algorithm.
- Put 3 layers of protection between employees and dangerous email messages.
- Don’t waste time on fussy configurations or adding threat reports. AI does that for you, getting everything up and running with just a few clicks and minimal maintenance.
- Click here to watch a video demo of Graphus now.










