How Does Ransomware Impact the Cost of a Data Breach?

Ransomware is at the forefront of any cybersecurity discussions these days. It’s also the root cause of many data breaches. In addition to the obvious upfront moneymaking purpose of a ransomware attack, cybercriminals also gain other assets that can be used to their advantage. Bad actors are always on the hunt for fresh stores of data that they can use to perpetrate further attacks or sell on the dark web for a handsome profit. There’s no specific type of data that they’re not interested in. Operational technology (OT), personal health information (PHI), personally identifying information (PII), financial data, trade secrets – they’re more than happy to snatch it all, leading to a consistent rise in data breaches caused by ransomware and a consistent wave of pain for businesses.
See 10 reasons why Graphus is better than other email security solutions. SEE THE LIST>>
Ransomware-Related Breaches Cost More Than the Average Breach
The IBM Cost of a Data Breach 2022 report offers some insight into the prevalence of ransomware-related data breaches, their growing price tag and the damage they can do to a business. It’s probably not a surprise, but the cost of a data breach has reached a new high, reaching $4.35 million this year. That’s a slight jump of 2.6% from the 2021 cost of $4.2 million per incident, which was at the time the highest ever recorded in the 17 years of the study. Many factors influence the cost of a data breach, and the presence of ransomware is one of them. The average cost of a ransomware-related data breach did dip slightly, from $4.62 million in 2021 to $4.54 million in 2022. However, ransomware is still more expensive than other data breaches with an average cost of $4.54 million, 19% higher than the average, not including any ransom paid.
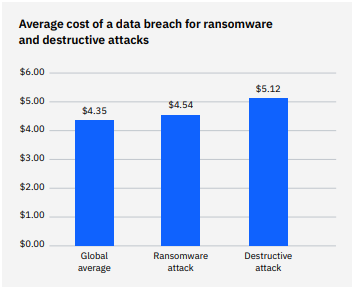
Source: IBM
Explore today’s biggest threats & what’s next in The State of Email Security 2022 GET IT>>
The Most Common Causes of a Data Breach May Surprise You
It’s important to note that ransomware is not the primary cause of a data breach. While it may soak up a lot of ink in the press, ransomware comes in third on the list of causes of a data breach. Ransomware was the culprit in 7.8% of breaches in the 2021 report, jumping to 11% in the 2022 study. So what’s the top cause of a data breach in this report? That honor goes to human error, the reason for almost one-quarter of the data breaches in this study. In second place, destructive attacks like wiper malware are at the root of 21% of breaches. The average cost of a destructive attack like that Is also above average, clocking in at $5.12 million, a difference of 16.3% from the average 2022 data breach cost. The list is rounded out by supply chain attacks, one-fifth of breaches were caused by a supply chain compromise or about 20% of the breaches that they analyzed.
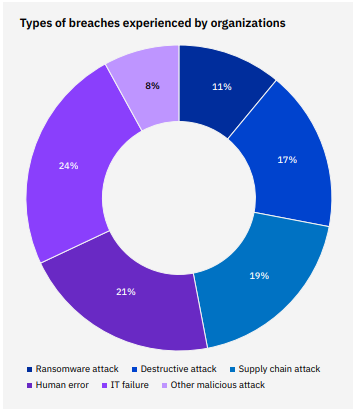
Source: IBM
AI is the secret weapon you’re looking for to boost business email security. SEE WHY>>
Ransomware Majorly Complicates Incident Response
A ransomware attack can be very complex, reaching far into a company’s IT systems and assets. Plus, highly skilled ransomware groups, like the kind that conduct nation-state attacks, can be very stealthy. Those factors make it much harder for businesses to detect and mitigate a ransomware-related data breach before serious damage is done. Researchers determined that the average time to identify and contain a ransomware attack is significantly higher than the identification and containment time for a breach caused by something else.
A data breach spawned by a ransomware attack takes the businesses an average of 237 days to identify and 89 days to contain, for a total lifecycle of 326 days. That’s 49 long, expensive, damaging days more than the 277 days in the incident response lifecycle of an average breach, a difference of 16.3%. That’s a big problem. The more time the bad guys have to hang around, the more damage they can do. In the case of another type of destructive attack, researchers determined that companies took 233 days to identify and 91 days to contain a breach, for a total lifecycle of 324 days. Additionally, organizations took 47 days longer to identify and contain a destructive attack, a difference of 15.6%.
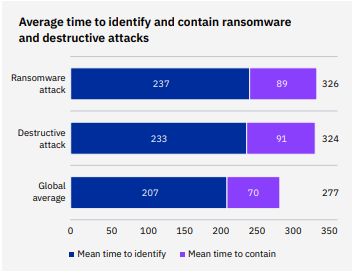
Source: IBM
See how ransomware rocks businesses in The Ransomware Road to Ruin. DOWNLOAD IT NOW>>
Does Paying the Ransom Make a Ransomware-Related Data Breach Cheaper?
It is slightly cheaper if the company pays the extortionists in a ransomware-caused data breach, but not. For those organizations that didn’t pay the ransom, the average cost of the breach was $5.12 million. For organizations that did pay the ransom, the cost of the breach was $4.49 million. The difference in average cost was $0.63 million, or 13.1%. Those cost estimates do not include any ransom amounts that businesses paid. This study’s ransomware breach’s cost was based on the necessary incident response activities like attack detection and loss of business due to system downtime. Regardless of the small difference in cost noted in this study, paying the bad guys is never a good idea and may land a company in even deeper hot water.
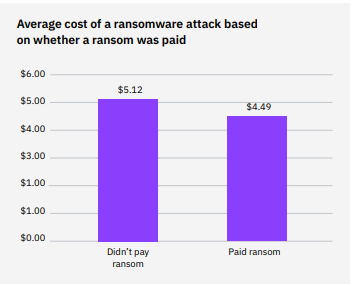
Source: IBM
See how to avoid cybercriminal sharks in Phishing 101. DOWNLOAD IT>>
Stop Wasting Money on Ineffective Email Security
In a recent survey, less than half of organizations ranked their current email security solutions as effective. That’s a sure path to disaster. However, companies that choose Graphus can feel confident that they’re protected from major sources of trouble by AI-enabled, automated email security that catches sophisticated phishing threats. They can also feel confident that they’re getting a great deal – Graphus is only about half of the cost of the competition.
These benefits make making the switch to Graphus an easy choice.
- Forget old-fashioned safe sender lists. Graphus analyzes the content of messages using more than 50 points of comparison to suss out fakes fast.
- Cloud-native security harnesses machine learning to inform AI using a patented algorithm.
- Put 3 layers of protection between employees and dangerous email messages.
- Don’t waste time on fussy configurations or adding threat reports. AI does that for you, getting everything up and running with just a few clicks and minimal maintenance.
Click here to watch a video demo of Graphus now.
NEW INTEGRATION! If you’re already using BullPhish ID for security and compliance awareness training and phishing simulations, you’ll love our latest integration Advanced Phishing Simulations (Drop-A-Phish). This feature leverages the power of integration with Graphus to eliminate the need for domain whitelisting and ensure 100% campaign deliverability to end users when running phishing simulations. LEARN MORE>>










