Double Encryption Ransomware Has Entered the Game
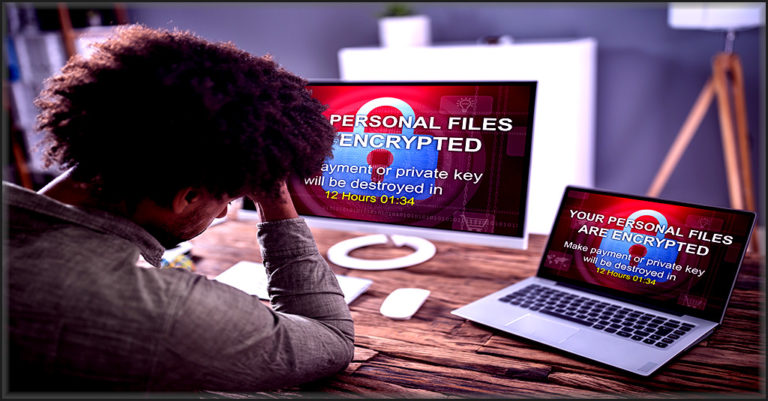
Ransomware is the biggest nightmare that most cybersecurity teams will ever have to face. An estimated 61% of organizations worldwide were victims of ransomware in 2020. This persistent threat is a favorite cybercriminal tool, used by cybercriminals of every stripe, from run-of-the-mill gangs to sophisticated nation-state threat actors – and it comes in a wide variety of styles. While many types of phishing attacks go in and out of style, the popularity of ransomware only grows – and its practitioners are always innovating.
Still relying on an old-fashioned SEG? See why Graphus is better! SEE THE COMPARISON>>
Know Your Enemy
By definition, ramsomware holds companies to ransom by encrypting their systems and data and demanding payment for regaining access to it,and a ransomware attack is usually kicked off with a phishing message. Learn more about ransomware and phishing threats here. Today’s nastiest cybersecurity villain comes in a variety of disguises, but in general, strains of ransomware will hew to one of two major categories:
Crypto Ransomware
Crypto ransomware encrypts data like files on a computer, making them unable to be accessed, using either symmetric or asymmetric file encryption. Cybercriminals will then offer to sell the victim the decryption key to unlock their data. This type of ransomware does not impact the machines it is used on, just the data. It’s the most prominent category that businesses will face, and almost always delivered through a phishing email.
Locker Ransomware
Locker ransomware makes devices unusable, like computers or machinery. The cybercriminals will then demand payment for a decryption key that unlocks the device upon payment of the ransom. This is the type of ransomware is often used in infrastructure attacks or attacks against manufacturing targets. While it is typically delivered with a phishing email like crypto ransomware, a locker ransomware incident may also be the result of a malicious insider incident.
Automated security isn’t a luxury. See why Graphus is a smart buy.
More Encryption, More Problems
The most popular variety of ransomware used these days is double extortion ransomware. Accounting for 50% of ransomware attacks in 2020, this variety can combine crypto and locker aspects to make one big mess for businesses. In a successful double extortion ransomware attack, the malware that the gang uses creates two distinct adverse effects for the victim, like encrypting data and locking machines at the same time. The gang then demands payment to undo both effects, like unlocking machines and decrypting data. A triple extortion variant creates three adverse effects.
But the newest player at the table is a little bit different: double encryption ransomware. This especially nasty version of crypto ransomware has two big advantages for cybercriminals. Check your domain’s risk for attacks like this >>
- Double encryption ransomware locks down data twice, allowing the victims access to the computers and all of their functions, but not their important data.
- That double lockdown enables bad actors to pull their typical double extortion trick by asking for two separate ransoms for two separate decryption keys.
What’s next in phishing? Find out in the 2021 State of Email Security Report! GET IT NOW>>
Double the Trouble
That’s where the twist that makes double encryption ransomware so nasty comes into play. When the victim interacts with the phishing message, it triggers a devastating consequence that is hard for any IT team to manage – two separate encryptions begin to spread, locking down the victim’s data in two different ways. This is becoming a trending threat to remote and hybrid teams because of their reliance on email. The double lockdown is more advantageous for cybercriminals because it means they’re more likely to get paid. Highly skilled recovery teams can sometimes crack the code that unlocks a victim’s data that’s been encrypted, but it’s a whole new ballgame when that data has been encrypted twice in two different ways.
Cybercriminals will typically use socially engineered spear phishing lures that include multiple “brands” of ransomware to infect the victim’s systems. Sometimes, the technique used is layered encryption. Data is first encrypted using one brand of ransomware, then re-encrypted using a second brand. For example, criminals may choose to use Babuk ransomware for one of the encryptions, then use REvil for the second. In another variant, the attackers will go for a side-by-side encryption style. They’ll infect some of the victim’s data with one brand of ransomware and the rest with another. Using the previous examples, the bad actors would use Babuk ransomware to encrypt some of the data, and REvil to encrypt the rest.
However the deed is accomplished, it’s a nightmare for any business. No matter what style of ransomware attack cybercriminals are using, they’re most likely to deliver it through a sophisticated phishing message. An estimated three-quarters of ransomware attacks arrive at a business attached to a phishing email. That means that the best way for businesses to avoid getting hit with a ransomware attack is to prevent phishing email from landing in employee inboxes where it could be unleashed in just one click – and the best way to accomplish that is Graphus.
Looking for a security rockstar? Get 5 superstar benefits at 1 low price! SEE THE BENEFITS>>
Three Layers of Powerful Protection from Ransomware
Graphus is the ideal choice for every business that wants to stop phishing email from reaching their staffers. Our smart, AI-powered protection gives companies three layers of powerful defense against phishing.
- TrustGraph analyzing over 50 different attributes of your employees’ communications to catch phishing emails before they ever hit an employee inbox – and we’re 40% better at it than our competitors.
- EmployeeShield places warning banners on messages that may be unwanted to alert employees to possible trouble when incoming communications fall outside of the company’s usual communication patterns.
- Phish911 empowers employees to report trouble with just one click if they receive a message that they find suspicious, sending it directly to quarantine, removing it from everyone else’s inbox and flagging it for administrator inspection.
Don’t wait until a nasty new variety of cyberattack like double encryption ransomware comes calling at your business. Set up a consultation with one of our solution specialists today and put Graphus to work for you in a flash.










